
FileZilla Website Distributes Malicious Installer
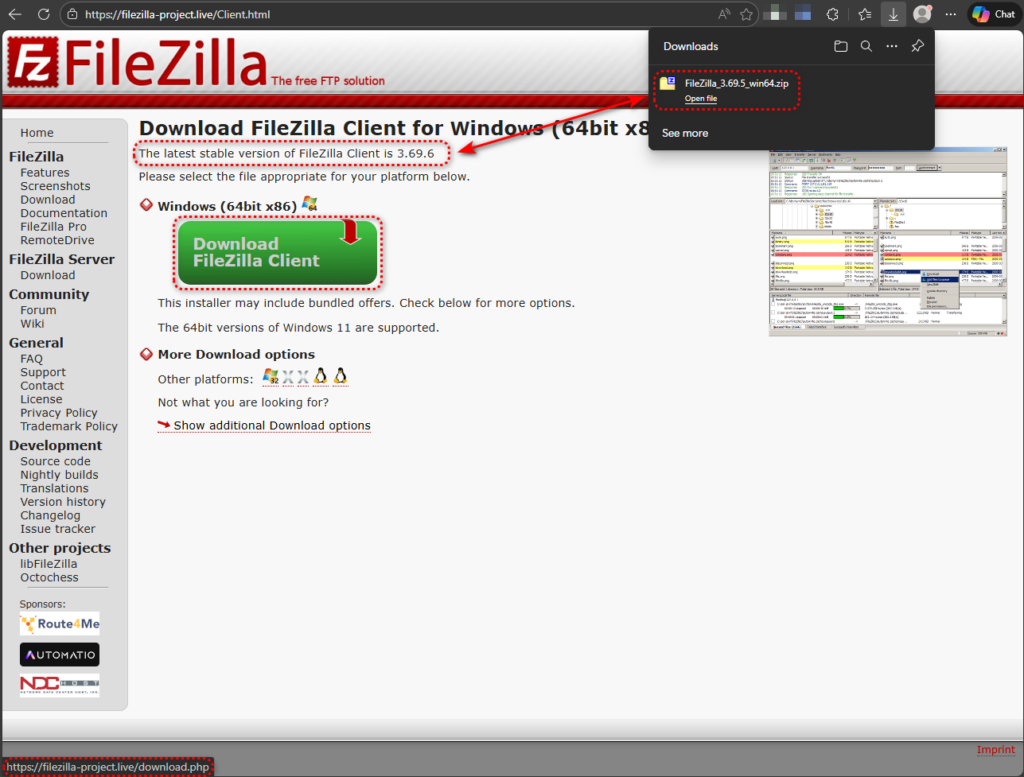
Cybersecurity researchers have uncovered a trojanized version of the popular open-source FTP client, FileZilla 3.69.5, circulating on deceptive websites.
This malicious archive mimics the legitimate portable release but includes a single harmful DLL file, enabling stealthy infection via DLL search order hijacking when users launch the application. The campaign highlights a rising trend of abusing trusted software to deliver advanced malware payloads.
Attack Mechanics
The malicious archive, hosted on a lookalike domain like filezilla-project[.]live, contains 918 files, of which 917 match the official FileZilla 3.69.5 portable release timestamp of 2025-11-12.
The outlier is version.dll, timestamped 2026-02-03, a system library absent from legitimate distributions. When filezilla.exe launches, Windows follows its DLL search order, prioritizing the application’s directory over System32, loading the trojanized version.dll first.
This technique, known as DLL search order hijacking (MITRE ATT&CK T1574.001), allows the malware to inject code into the legitimate process without altering the executable.
Process Monitor analysis confirms this: for system DLLs like IPHLPAPI.DLL, Windows falls back to System32 after a “NAME NOT FOUND” in the app directory, but version.dll loads directly from the tampered folder. The DLL then attempts to proxy calls to a missing version_original.dll, potentially causing instability while maintaining functionality to evade detection.
Evasion and Anti-Analysis Features
The version.dll incorporates robust anti-analysis measures to thwart sandboxing and virtualization. It performs BIOS version checks, queries system manufacturers, probes VirtualBox registry keys, enumerates disk drives, and uses write-watch memory allocation to detect scanning tools. Evasive sleep loops further delay execution in suspicious environments.
In controlled tests mimicking real systems, the loader resolved its C2 domain and initiated callbacks; in obvious VMs, it abruptly terminated FileZilla. These selective checks ensure payload deployment only on likely victim machines, reducing forensic footprints.
Command-and-Control Operations
Once activated, the malware employs DNS-over-HTTPS (DoH) for stealthy domain resolution, querying Cloudflare’s 1.1.1.1 resolver. This bypasses traditional DNS monitoring on port 53, a tactic echoing recent fake 7-Zip campaigns.
Resolved domains lead to callbacks, with embedded JSON config: {“tag”: “tbs”, “referrer”: “dll”, “callback”: “https://welcome.supp0v3.com/d/callback?utm_tag=tbs2&utm_source=dll”}.
A secondary channel targets 95.216.51[.]236:31415 on Hetzner infrastructure, retrying connections to persist C2 access. UTM parameters indicate a coordinated operation with multiple infection vectors.
Broader Capabilities and Risks
Behavioral analysis reveals credential harvesting from FTP servers, process injection via suspended processes and memory writes, .NET compilation with csc.exe, autorun registry persistence, and file-encryption APIs.
While some detections may overlap with FileZilla’s legitimate actions, C2 integration confirms malicious intent. Stolen FTP credentials threaten connected servers, amplifying supply-chain risks.
This fits a pattern: fake 7-Zip archives turned PCs into proxies last month, and Notepad++ updates delivered backdoors via sideloading. Attackers exploit user trust in portable apps, distributed via search poisoning and impersonator domains.
Detection and Mitigation
Inspect the FileZilla Portable folders for version.dll; its presence signals a compromise. Download only from filezilla-project. od verifying SHA-256 hashes.
| Type | Indicator | Description |
|---|---|---|
| SHA-256 (Archive) | 665cca285680df321b63ad5106b167db9169afe30c17d349d80682837edcc755 | Trojanized FileZilla_3.69.5_win64.zip |
| SHA-256 (DLL) | e4c6f8ee8c946c6bd7873274e6ed9e41dec97e05890fa99c73f4309b60fd3da4 | Malicious version.dll |
| Domain | filezilla-project[.]live | Fake download site |
| IP: Port | welcome.supp0v3[.]com | C2 callback/staging server |
| IP:Port | 95.216.51[.]236:31415 | Secondary C2 on Hetzner infrastructure |
Check ZIP timestamps pre-extraction for anomalies. Enable application allowlisting and network segmentation. Enterprises should scan for MITRE techniques T1218.011 (DLL Injection), T1071.001 (Web Protocols C2).
DLL sideloading persists due to entrenched Windows behaviors and portable app popularity. Open-source tools face repeated abuse, underscoring the need for hash verification, official sources, and behavioral monitoring.
As DoH evades legacy defenses, adopt encrypted DNS inspection and endpoint-detection rules to detect anomalous DLL loads. Users, with high FileZilla adoption for web development, face elevated risks from search-driven downloads.
Site: cybersecuritypath.com
Reference: said


