China-Nexus Hackers Launch New Malware Attacks on Telecom Networks
China-linked threat actors known as UAT-9244 have escalated attacks against South American telecom providers, deploying three sophisticated malware implants to burrow deep into networks.
Since 2024, this advanced persistent threat (APT) group has targeted Windows endpoints, Linux servers, and edge devices, seeking long-term espionage access.
An uncovered the operation, linking UAT-9244 with high confidence to the notorious Famous Sparrow APT and overlaps with Tropic Trooper, both China-aligned groups known for cyberespionage.
Unlike the recent Salt Typhoon telecom hacks, no direct ties exist here, but the focus on critical infrastructure raises alarms for regional stability.
TernDoor: Evolving Windows Backdoor
TernDoor marks UAT-9244’s primary Windows weapon a fresh twist on the CrowDoor backdoor, itself an upgrade from Famous Sparrow’s SparrowDoor.
Attackers kick off with DLL side-loading: a legitimate “wsprint.exe” loads the malicious “BugSplatRc64.dll,” which decrypts “WSPrint.dll” using the key “qwiozpVngruhg123” and unleashes TernDoor in memory.
Key upgrades include unique command codes and an embedded AES-encrypted Windows driver (WSPrint.sys) for process suspension, resumption, or termination,n ideal for dodging detection. The driver masquerades as a service, creating a hidden device “\Device\VMTool” to manipulate processes stealthily.
Persistence comes via scheduled tasks (“WSPrint” running as SYSTEM on startup) or Registry Run keys, with tweaks to hide the task from view.
TernDoor phones home to C2 servers over port 443, grabs configs for IPs, ports, and User-Agents, then executes commands, steals system info, reads/writes files, or self-uninstalls with the “-u” switch.
PeerTime: P2P Chaos on Linux
Shifting to Linux, PeerTime (aka angrypeer) thrives on embedded systems like ARM and MIPS architectures, perfect for telecom edge gear.
A shell script drops a loader and instrumentor; the latter sniffs for Docker and runs the loader inside if found, complete with Simplified Chinese debug strings hinting at native developers.
The loader decrypts and runs PeerTime in memory, renaming itself to blend as a legit process. It hijacks BitTorrent protocols for C2 discovery, peer file downloads, and execution writing payloads via BusyBox to disk. Versions exist in C/C++ and newer Rust for efficiency.
This P2P design lets it evade traditional C2 blocks, pulling commands from distributed nodes while staying resilient.
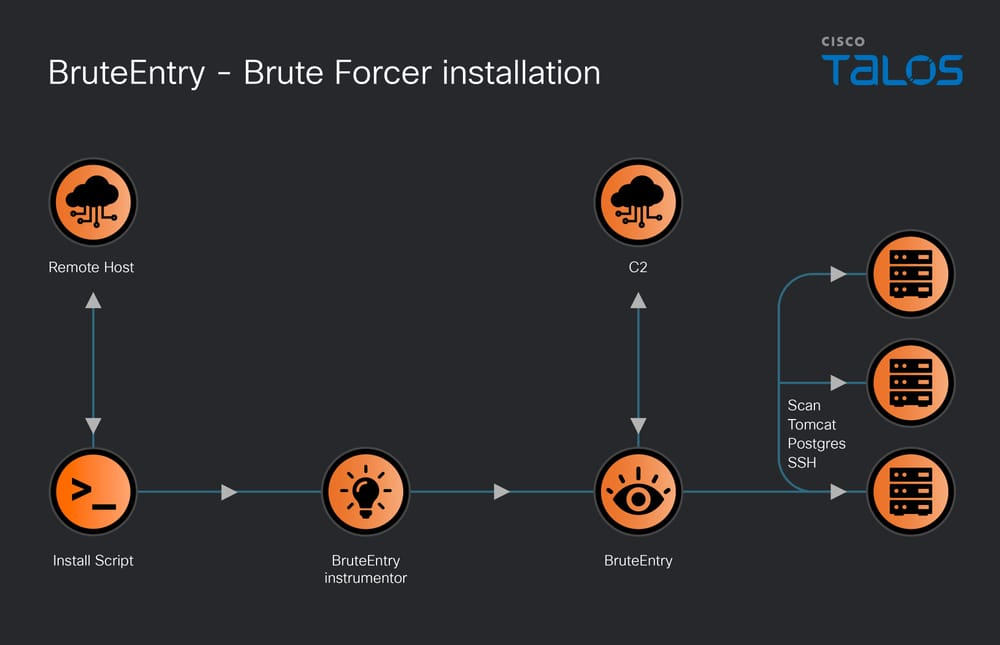
BruteEntry: Building ORB Armies
BruteEntry turns hacked edge devices into “Operational Relay Boxes” (ORBs) proxy scanners brute-forcing SSH, Postgres (port 5432), and Tomcat (/manager/html). A GoLang instrumentor checks for running instances via pgrep, then launches the agent.
The agent registers with C2 via JSON (IP, hostname), gets an agent_id, and pulls up to 1,000 target IPs per task batch. It slams embedded credential lists against services, reporting hits like “Cracked by agent X | Version Y” or failures as “All credentials tried.”
Successes feed UAT-9244’s broader botnet, chaining compromises across the internet.
| Implant | Platform | Key Technique | Evasion/Persistence | C2 Method |
|---|---|---|---|---|
| TernDoor | Windows | DLL side-loading, driver | Process manip, scheduled task | HTTP/443 |
| PeerTime | Linux | P2P BitTorrent | Docker exec, process rename | Peer-to-peer |
| BruteEntry | Linux | Brute-force scanning | ORB proxy chaining | JSON API tasks |
Defense and IOCs
Defenders should hunt for ClamAV sigs like Win.Malware.TernDoor and Snort SID 65551, plus block C2s like 154.205.154.82:443 and 212.11.64.105. Patch edge devices, monitor DLL loads, and scan for ORB traffic spikes.
This campaign’s cross-platform toolkit and P2P innovation signal escalating threats to telecoms, prompting action that can blunt UAT-9244’s edge.
Site: https://cybersecuritypath.com
Source: Said by Cisco Talos