Critical Chrome Security Flaw Let Malicious Extensions Take Over Gemini AI Panel
Google Chrome’s shiny new Gemini AI side panel just dodged a bullet. An uncovered a high-severity flaw, CVE-2026-0628, that let rogue browser extensions hijack the panel and unlock god-like powers over your machine.
Think unauthorized camera access, file grabs, and screenshots all without your okay. Google patched it quietly in early January 2026 after a responsible disclosure in October 2025.
But the scare spotlights a bigger headache: as browsers get “smarter” with AI, they’re cracking open new doors for attackers.
AI Browsers: Power and Peril in One Package
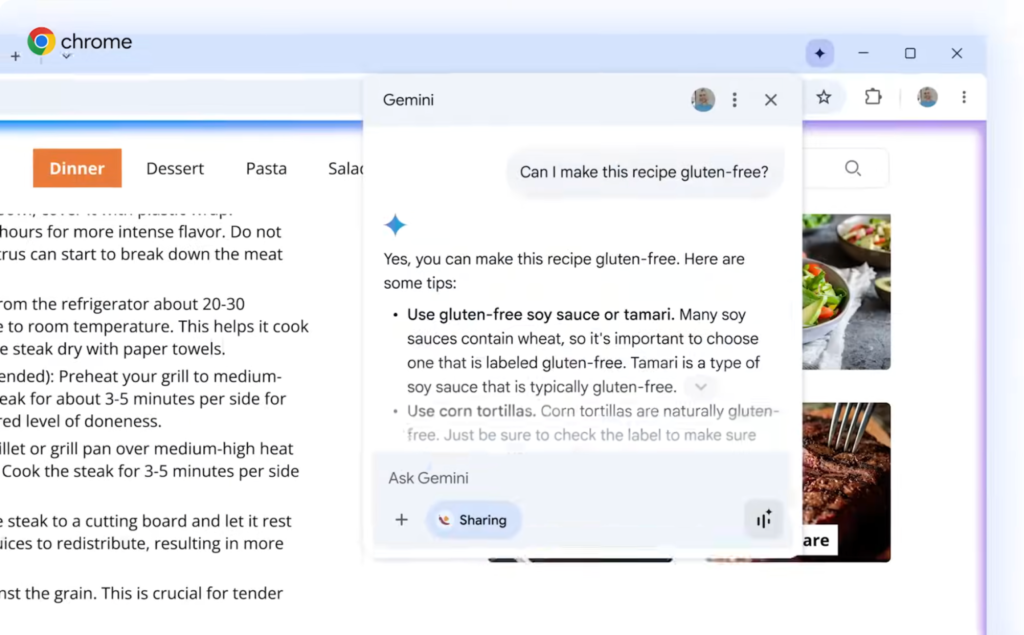
You’re browsing, hit the Gemini button in Chrome’s title bar, and a sleek side panel pops up. Powered by Google’s Gemini Live, it summarizes pages, automates tasks, and even chats contextually about what you’re seeing.
It’s part of a trend called “agentic browsers,” think Chrome’s Gemini, Edge’s Copilot, or newcomers like Atlas. These tools give AI a front-row seat to your screen, blending multimodal smarts (text, images, voice) with browser privileges.
By fusing AI directly into the browser, Google created a juicy target. Malicious sites could already try “prompt injection” tricks to trick the AI, as seen in prior research. Worse, this flaw lets low-privilege extensions punch way above their weight.
Malicious Extensions Take Over Gemini AI Panel
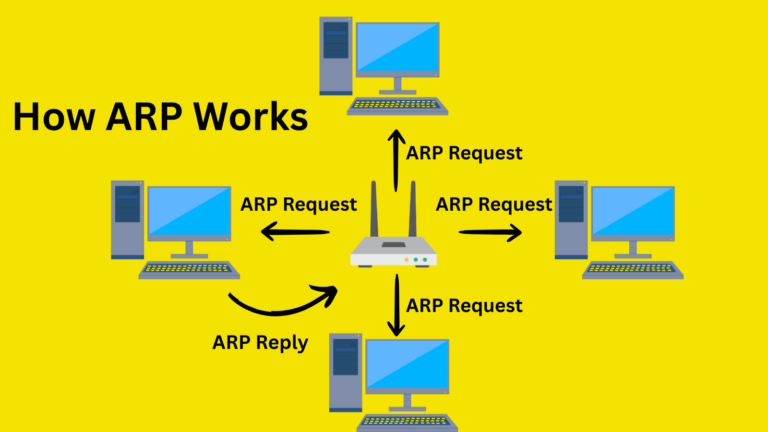
Browser extensions live by strict rules. They declare permissions like blocking ads via the declarativeNetRequests API and stay sandboxed. They can tweak web traffic on normal tabs, sure.
But they shouldn’t mess with core browser components like the Gemini panel, which loads https://gemini.google.com/app in a privileged context.
That’s where CVE-2026-0628 struck. A basic extension could intercept and inject JavaScript into the panel’s load process. Chrome failed to properly isolate the panel from extension hooks on that specific URL.
Once injected, the code ran with the panel’s elevated rights, no extra clicks needed.
| Component | Normal Privileges | Flaw Impact |
|---|---|---|
| Standard Web Tab | Low (SOP-enforced) | Extensions can inject JS (expected behavior) |
| Gemini Side Panel | High (camera, mic, files, screenshots) | Extensions hijack → full privilege escalation |
| Extension Itself | Basic API access only | Gains panel powers without user consent |
This isn’t theoretical. A shady extension fires up your camera/mic silently, snaps HTTPS tab screenshots, raids local files, or even spins up phishing pages in the trusted panel. All triggered by just opening Gemini.
This echoes nasty extension attacks we’ve seen before, such as the 2024 hijacking of 35 legitimate Chrome extensions that stole credentials from millions. Or the surge in malicious store listings, per GitLab’s 2025 report.
In enterprises, imagine attackers quietly filming meetings or exfiltrating sensitive docs. No pop-ups, no drama, just stealthy escalation.
- Oct 23, 2025: Disclosure to Google.
- Early Jan 2026: Patch rolled out (pre-public reveal).
Users on updated Chrome are safe. But it raises alarms for unpatched fleets or sideloaded extensions.
Why This Matters
Agentic browsers promise to “do stuff for you”, booking flights, debugging code, whatever. But privileges like screen-scraping and hardware access amplify risks.
Developers must harden isolation: tighter URL scoping, extension-panel firewalls, and AI-specific sandboxing.
This flaw proves AI integration isn’t plug-and-play. As Chrome evolves, expect more scrutiny. For now, audit your extensions, enable auto-updates, and watch for “helpful” ones asking odd permissions. The browser arms race just got smarter and scarier.
Site: https://cybersecuritypath.com
Reference: Said by Paloltonetworks