
Malicious Go “crypto” Module Harvests Credentials and Deploys Rekoobe Backdoor
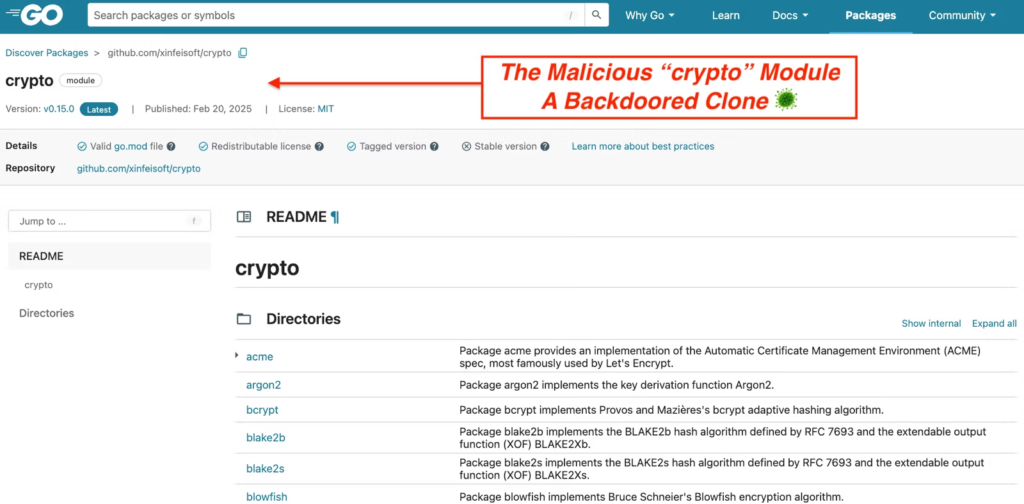
A sophisticated supply chain attack targeting Go developers through a malicious module impersonating the trusted golang.org/x/crypto library.
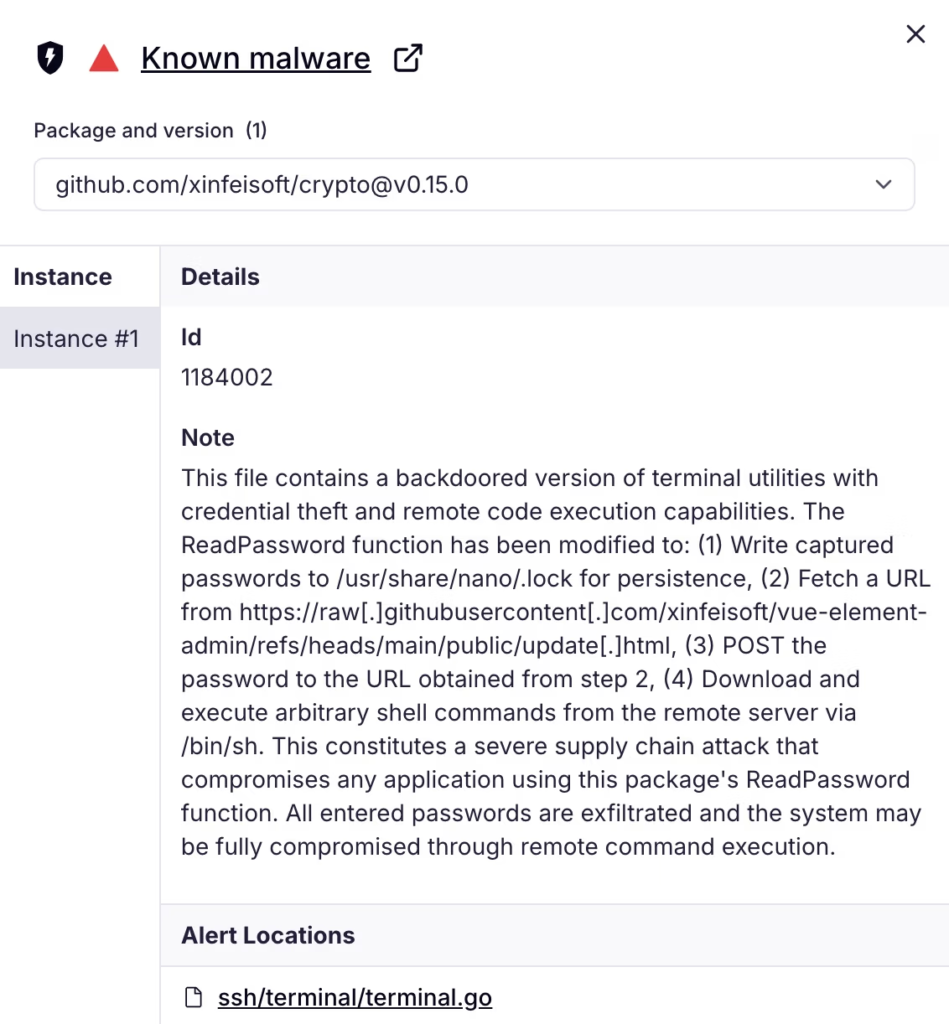
This package mirrors the legitimate codebase but embeds a backdoor in the ssh/terminal/terminal.go file.
The attack leverages the high-trust status of golang.org/x/crypto, which provides critical primitives like bcrypt, argon2, chacha20, and SSH functionality, making it a prime impersonation target in dependency graphs.
Backdoor Mechanics
The malicious code activates during interactive password prompts via the ReadPassword function.
When invoked, it captures the entered secret using the term.ReadPassword echoes it to /usr/share/nano/.lock for persistence, fetches a staging URL from raw.githubusercontent.com/xinfeisoft/vue-element-admin/refs/heads/main/public/update.html, and POSTs the credentials to a threat actor endpoint retrieved from that resource.
It then downloads and executes a shell script via /bin/sh, initiating the next infection stage. This design ensures stealth, triggering only during real-world use, such as SSH authentication or database logins, thereby evading non-interactive tests.
The module depends on github.com/bitfield/script, a legitimate library for HTTP requests and shell pipelines, which facilitates the network activity and command execution without raising immediate suspicion. On pkg.go.dev, it appears as a standard crypto library with familiar subpackages, blending seamlessly into go.mod files.
Infection Chain
The exfiltrated script serves as a Linux stager, targeting Ubuntu-like environments. It appends a hardcoded threat-actor SSH public key to /home/ubuntu/.ssh/authorized_keys for persistent remote access, sets iptables policies to ACCEPT for both INPUT and OUTPUT to weakenthe firewalls, and stages payloads from img. spoolsv.cc disguised as .mp5 media files.
The chain unfolds in five stages post-trigger:
- GitHub Raw fetch resolves to seed.php.
- seed.php returns snn50.txt, a curl | sh launcher.
- snn50.txt installs SSH key, turns off firewall defaults, downloads sss.mp5 and 555.mp5, executes them in /tmp, and cleans up artifacts.
sss.mp5 (SHA256: 4afdb3f5914beb0ebe3b086db5a83cef1d3c3c4312d18eff672dd0f6be2146bc) acts as a loader, probing connectivity to 154.84.63.184:443 without standard TLS handshakes. 555.mp5 (SHA256: 8b0ec8d0318347874e117f1aed1b619892a7547308e437a20e02090e5f3d2da6) is confirmed as Rekoobe, a versatile Linux backdoor linked to APT31 operations, enabling file theft, payload downloads, and reverse shells over a custom TCP channel on port 443.
Threat Actor Infrastructure
The xinfeisoft GitHub account orchestrates the campaign with four repositories: crypto (malicious module), vue-element-admin (staging via update.html, updated July 12, 2025, from .net to .cc endpoints), demo, and feisoft.
This setup uses GitHub Raw for dynamic C2 indirection, mimicking developer traffic while allowing infrastructure rotation without module republishing. The account remains active despite abuse reports.
Mitigation and Response
After Socket’s report, the Go security team blocked the module on the public proxy, returning 403 SECURITY ERROR, though it lingered in caches until at least December 16, 2025. Defenders must treat go.mod/go.sum as security boundaries, scanning for anomalous dependencies like bitfield/script in crypto contexts.
Recommendations include:
- Deploy GitHub App, CLI, Firewall, browser extension, and MCP for PR scans, CI enforcement, and AI workflow protection.
- Monitor for IOCs: credential writes to /usr/share/nano/.lock, GitHub Raw fetches followed by dynamic POSTs, authorized_keys mods, iptables changes.
- Map to MITRE ATT&CK: T1195.002 (Supply Chain), T1056 (Input Capture), T1098.004 (SSH Keys), T1562.004 (Firewall Impair).
This low-effort, high-impact tactic namespace confusion via trusted mirrors signals rising threats to credential-edge libraries in Go and beyond. Expect variants targeting SSH helpers and CLI prompts.
Indicators of Compromise
Site: cybersecuritypath.com



