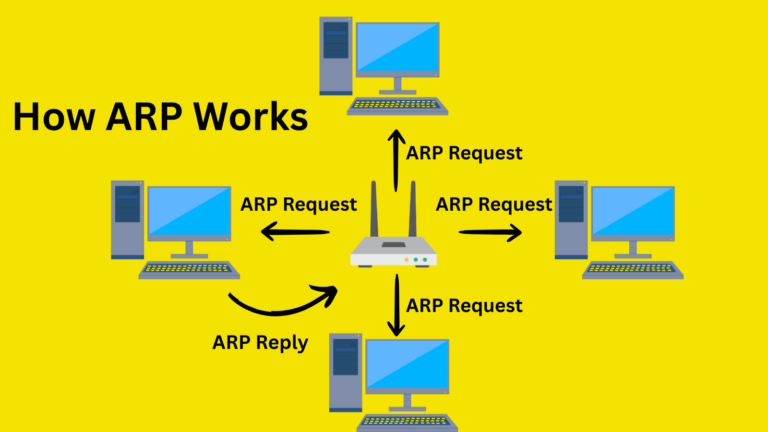
Cybersecurity firm Arctic Wolf has detected threat actors exploiting CVE-2025-32975, a critical authentication bypass vulnerability in Quest KACE Systems Management Appliance (SMA), to gain full administrative control over vulnerable systems.
This flaw, patched in May 2025, allows attackers to impersonate legitimate users without credentials via flawed SSO handling, earning a perfect CVSS score of 10.0. No public proof-of-concept existed prior, and related vulnerabilities (CVE-2025-32976 to -32978) show no evidence of abuse, yet exploitation surged in March 2026, targeting unpatched instances.
Quest KACE SMA is an on-premises tool for endpoint management, inventory, and patching, prime real estate for attackers eyeing network dominance.
Discovered by Seralys researchers in April 2025, CVE-2025-32975 resides in SSO authentication, enabling remote, unauthenticated admin takeover (CVSS: AV:N/AC:L/PR:N/UI:N/S:C/C:H/I: H/A : H). Quest coordinated fixes post-disclosure, but delayed patching left systems exposed, especially internet-facing ones.
Exploitation likely started with CVE-2025-32975, delivering rapid admin privileges. Attackers abused KPluginRunProcess, a KACE feature for running remote commands, to run malicious payloads. Logs revealed Base64-encoded commands, followed by curl downloads from IP 216.126.225.156 for C2 setup.
Persistence kicked in via runkbot.exe (KACE’s script runner), creating backdoor admins:
net localgroup administrators ooo1 /addnet group "domain admins" ooo2 /add
Stealthy PowerShell executed: powershell -ExecutionPolicy Bypass -WindowStyle Hidden -File "C:\temp\Enable-UpdateServices.ps1". Taskband.ps1 altered the registry for permanent access.
Credential dumping used Mimikatz (as asd.exe). Discovery spanned:
- Local:
queser.exe(users),net localgroup administrators,net user. - Domain:
net group "domain admins" /domain > c:\1.txt,net group "domain controllers" /domain,net time /domain.
Lateral movement hit RDP on Veeam/Veritas backups and domain controllers.
| Product | Affected Versions | Fixed Versions |
|---|---|---|
| Quest KACE SMA | 13.0.x < 13.0.385 13.1.x < 13.1.81 13.2.x < 13.2.183 14.0.x < 14.0.341 (Patch 5) 14.1.x < 14.1.101 (Patch 4) | 13.0.385+ 13.1.81+ 13.2.183+ 14.0.341 (Patch 5)+ 14.1.101 (Patch 4)+ |
Follow organizational testing to avoid disruptions.
- Patch urgently: Apply fixes from Quest’s advisory.
- Isolate exposure: Remove public internet access; mandate VPN/firewall for remote needs.
- Hunt IOCs: Monitor for IP 216.126.225.156, commands, Mimikatz, and new admins like “ooo1”.
- Best practices: Enforce MFA, logging, EDR; scan for exposed KACE via Shodan.
This breach, hitting sectors such as education, highlights the risks of legacy management tools. Organizations delaying patches face ransomware or espionage.
Site: cybersecuritypath.com