The Address Resolution Protocol (ARP) maps IP addresses to MAC addresses in local networks, enabling data link layer communication. This foundational protocol, defined in RFC 826 since 1982, operates without authentication, creating significant cybersecurity risks, such as spoofing attacks.
ARP resolves layer-3 IP addresses to layer-2 MAC addresses within a single broadcast domain, such as a LAN. It functions at the data link layer, encapsulated directly in Ethernet frames with EtherType 0x0806. Unlike routable protocols, ARP never crosses routers, limiting its scope to local segments.
Hosts maintain an ARP cache, a temporary table of IP-to-MAC mappings to avoid repeated resolutions. Entries expire after a timeout, typically 2-20 minutes, depending on the OS, prompting the system to issue new queries. This cache optimizes performance but introduces vulnerabilities when manipulated.
ARP packets are 28 bytes for Ethernet/IPv4, comprising a header and four address fields. Key fields include:
| Field | Size (bits) | Description |
|---|---|---|
| Hardware Type (HTYPE) | 16 | Link layer type (1=Ethernet) |
| Protocol Type (PTYPE) | 16 | Network layer (0x0800=IPv4) |
| Hardware Length (HLEN) | 8 | MAC size (6 bytes) |
| Protocol Length (PLEN) | 8 | IP size (4 bytes) |
| Operation (OPER) | 16 | 1=request, 2=reply |
| Sender Hardware Addr | 48 | Sender MAC |
| Sender Protocol Addr | 32 | Sender IP |
| Target Hardware Addr | 48 | Target MAC (zeros in request) |
| Target Protocol Addr | 32 | Target IP |
In requests, the target hardware address is set to all zeros because it’s unknown. Replies fill all fields accurately.
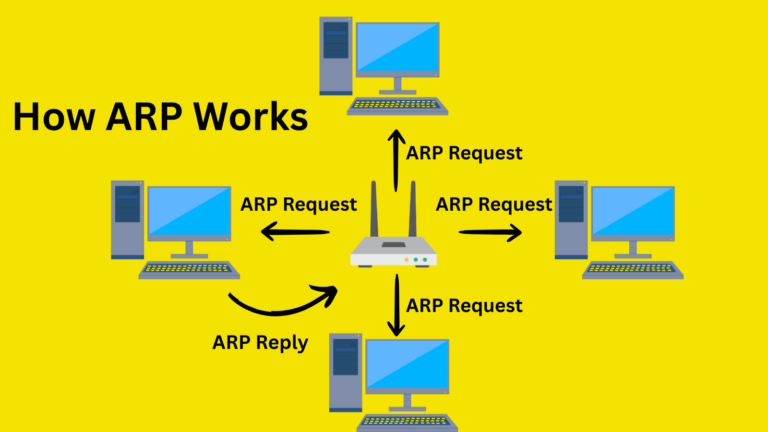
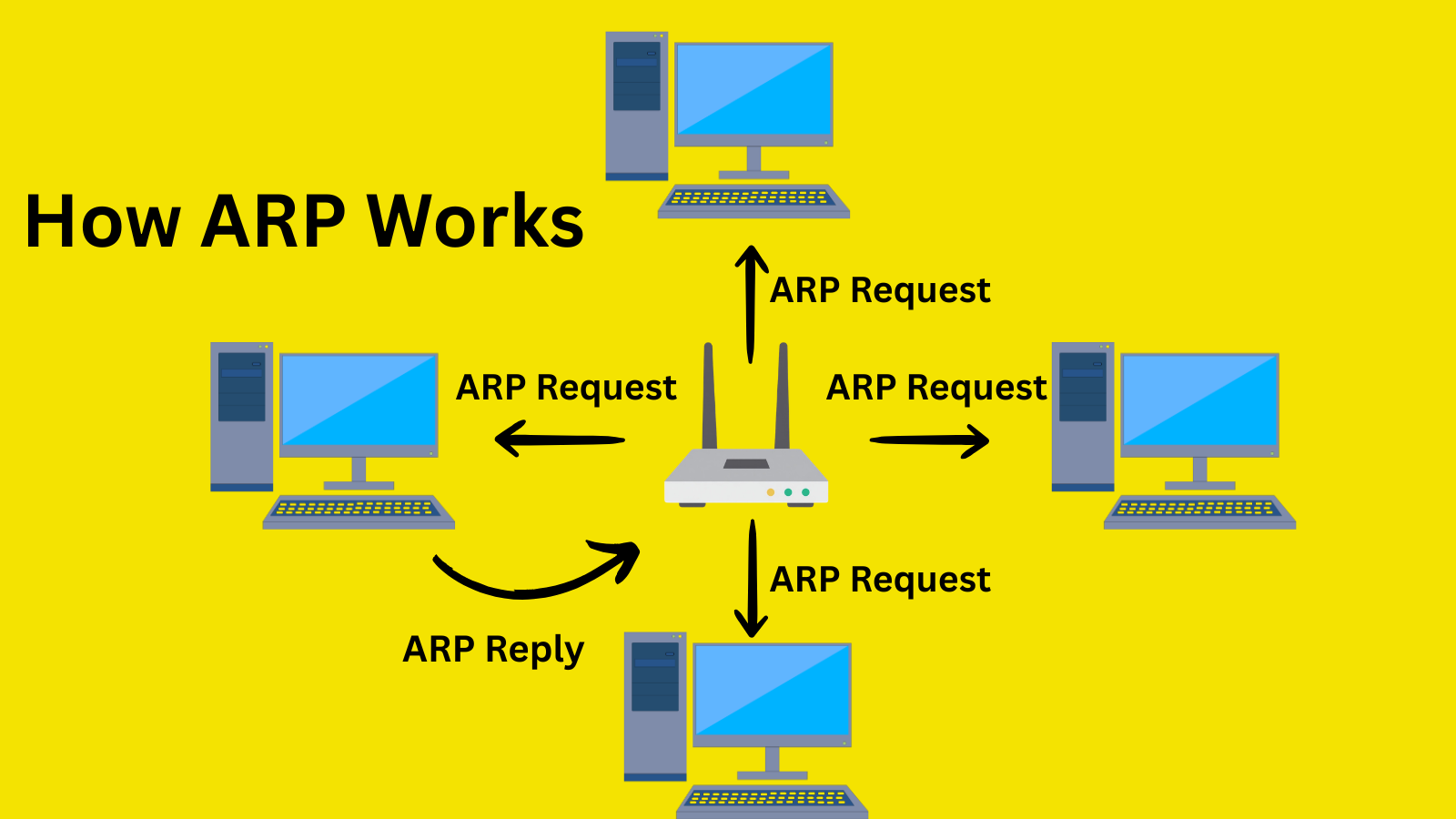
How ARP Works
ARP begins with a cache check: if the destination IP address maps to a valid MAC address, the host uses it immediately. Absent an entry, it broadcasts an ARP request: “Who has IP 192.168.1.10? Tell 192.168.1.5.”
The Ethernet frame uses the destination MAC FF:FF:FF:FF:FF:FF (broadcast) and the sender’s source MAC. All local devices receive it; only the matching IP host unicasts a reply with its MAC. The sender caches this for future use, completing resolution in milliseconds.
Gratuitous ARP occurs when a host broadcasts its own IP-MAC pair (TPA=SPA, THA=zeros), updating neighbors’ caches during IP changes or duplicate detection.
ARP Cache Mechanics
Caches store entries as {IP: MAC, timestamp}, and update them on replies regardless of the request. Hosts like Linux are used arp -n for inspection; Windows uses arp -a. Static entries can be added manually for critical mappings to prevent dynamic overrides.
Probes use all-zero sender fields to detect IP conflicts before assignment. Caches overwrite old entries on new replies, enabling poisoning without expiration waits.
ARP lacks authentication: any device can reply with forged ARP mappings, since the protocol trusts all responses. This stateless design suits performance but exposes networks to spoofing.
Common exploits include gratuitous ARP floods that gradually poison caches. No sequence numbers or signatures verify legitimacy, making native verification impossible.
ARP Spoofing and Poisoning Attacks
ARP spoofing sends unsolicited replies that associate the attacker’s MAC address with a victim’s IP address. In a man-in-the-middle (MitM) attack, attackers poison both the source (e.g., the victim) and gateway caches, relaying traffic while inspecting/modifying it.
Tools like ArpSpoof or Ettercap automate this: scan for IPs, then flood replies faster than legitimate ones. Impacts include data interception, session hijacking, DoS via traffic drops, or malware injection.
In a typical attack, the attacker (192.168.1.100) spoofs the gateway (192.168.1.1)’s IP to the victim’s MAC cache, and the victim’s IP to the gateway’s cache. Victim’s outbound traffic hits the attacker, who forwards it to the real gateway, enabling eavesdropping on unencrypted protocols like HTTP.
Detection Techniques
Monitor for anomalies: duplicate IPs in ARP tables, excessive replies, or MAC changes for IPs. Tools like Wireshark filter “arp.duplicate-address-detected” or arpwatch log changes.
IDS/IPS scan for rapid gratuitous ARPs or non-request replies. Compare ARP tables across hosts; mismatches indicate poisoning. Passive monitoring tools like XArp detect spoofing via traffic analysis.
Prevention and Mitigation Strategies
Dynamic ARP Inspection (DAI): Cisco switches validate ARP against DHCP snooping bindings, dropping invalid packets. Static ARP Entries: Manually bind critical IPs (e.g., gateways) to MACs.
Network Segmentation: VLANs limit broadcast domains and contain attacks. Encryption: Use HTTPS, VPNs (e.g., IPsec), or WPA3 to protect payloads even if they are intercepted.
Tools: ArpON for inspection modes (SARPI/DARPI), blocking spoofed packets. Intrusion prevention with anomaly detection flags suspicious activity.
IPv6 replaces ARP with the Neighbor Discovery Protocol (NDP), using ICMPv6 with cryptographic options such as SEND for authentication. Secure variants include ARP-SNMP integration or blockchain-based ledgers, though not widespread.
In cybersecurity, zero-trust models bypass ARP reliance through overlay networks like SD-WAN. Monitoring suites (SolarWinds, Wireshark) provide proactive defense.
ARP remains essential but demands layered defenses in 2026’s threat landscape. Implementing DAI and monitoring significantly reduces risks.