Microsoft has deployed an out-of-band (OOB) update, KB5085516, for Windows 11 versions 25H2 (OS Build 26200.8039) and 24H2 (OS Build 26100.8039), released on March 21, 2026, that addresses a critical sign-in disruption introduced by the prior March 10 Patch Tuesday update, KB5079473.
This cumulative patch rolls in previous security and non-security fixes while resolving the authentication issue affecting consumer Microsoft account users.
The flaw stemmed from KB5079473, which inadvertently blocked sign-ins to Microsoft apps like Teams Free, OneDrive, Outlook.com, and Edge using personal Microsoft accounts, displaying a false “no Internet” error even when connectivity was present.
Enterprise users relying on Microsoft Entra ID remained unaffected, limiting the blast radius to individual consumers and hybrid setups. Cybersecurity experts warn that such disruptions create prime phishing opportunities, as frustrated users may bypass security measures through risky workarounds.
This OOB arrives amid Microsoft’s March 2026 security push, which included KB5079473, which patched 58-79 vulnerabilities, including two zero-days, and emphasized rapid response to regressions. No new exploits tied directly to the sign-in bug have surfaced, but it compounded the risks posed by unpatched systems exposed to earlier flaws.
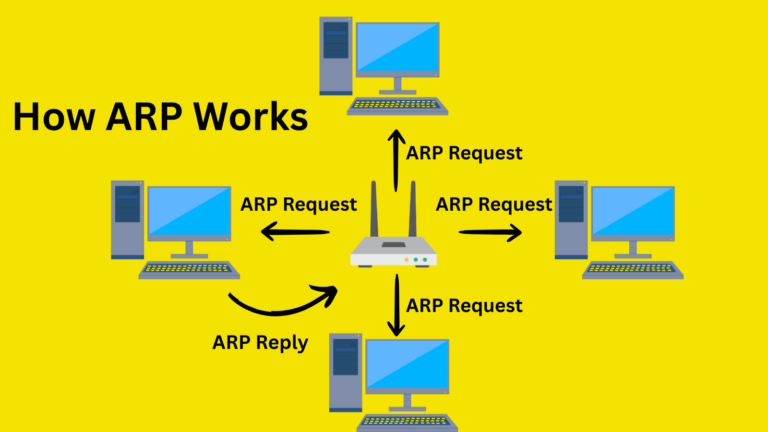
While KB5085516 focuses on usability, it builds on the defenses in KB5079473 against severe Remote Code Execution (RCE) flaws in Windows Routing and Remote Access Service (RRAS), which are critical for VPNs and enterprise routing. Attackers could leverage integer overflows in RRAS for heap buffer overflows, enabling arbitrary code execution over networks with low complexity.
A separate hotpatch KB5084597 (March 13) addressed these issues without requiring reboots on eligible devices, underscoring RRAS’s appeal to threat actors targeting on-premises infrastructure. Proof-of-concept exploits for some CVEs heighten urgency, potentially aiding lateral movement in domains.
Admins can push KB5085516 via Windows Update (optional section), Microsoft Update Catalog, Intune, or Autopatch expedite for enterprises. It includes Servicing Stack Update KB5083532 for reliable patching and bumps AI components such as Image Search, Content Extraction, and Semantic Analysis to version 1.2602.1451.0, boosting on-device intelligence without introducing new vulnerabilities.
No known issues post-install; Microsoft urges enabling “Get the latest updates as soon as they’re available.” Rollback risks undoing security gains, per guidance.
For cybersecurity pros like those in threat intelligence, this chain of zero-day patches inducing regressions, swift OOB fixes highlights Windows servicing’s dual-edged sword: robust but brittle under rapid iteration. Unpatched RRAS setups remain high-value targets for RCE chains, especially in legacy VPNs; scan environments now. Consumers regain seamless access to cloud services, reducing shadow IT risks.
Prioritize OOB deployment to maintain hygiene amid escalating state-sponsored RRAS probes. Monitor Windows Release Health for exploits. This episode reinforces: Patch regressions fast to avoid amplifying vulnerabilities.
Site: cybersecuritypath.com