
Technical Analysis: Uncovering the Monero Mining Malware Operation
This technical article examines a sophisticated Monero cryptojacking campaign identified in late 2025, featuring advanced persistence and kernel exploitation. It draws from forensic analysis of the “Explorer.exe” controller and associated payloads.
Cryptojacking has evolved into a persistent threat prioritizing hashrate maximization through multi-stage infections. This operation uses redundant watchdogs, worm propagation via USB, and BYOVD via WinRing0x64.sys (CVE-2020-14979) for Ring 0 access.
The campaign spreads via pirated software lures, deploys XMRig miners disguised as system processes, and employs anime-inspired command modes, such as “002 Re:0,” to enhance resilience.
Attackers distribute droppers as fake office suite installers, tricking users into execution (T1204.002). Upon launch, Explorer.exe (MD5: bb97dfc3e5fb8109bd154c2b2b2959da) self-copies to C:\Users%USERNAME%\explorer.exe and enters active mode.
No remote C2 downloads occur; payloads are extracted from PE resources (ID 120), decompressed,d and hidden with FILE_ATTRIBUTE_HIDDEN|SYSTEM.
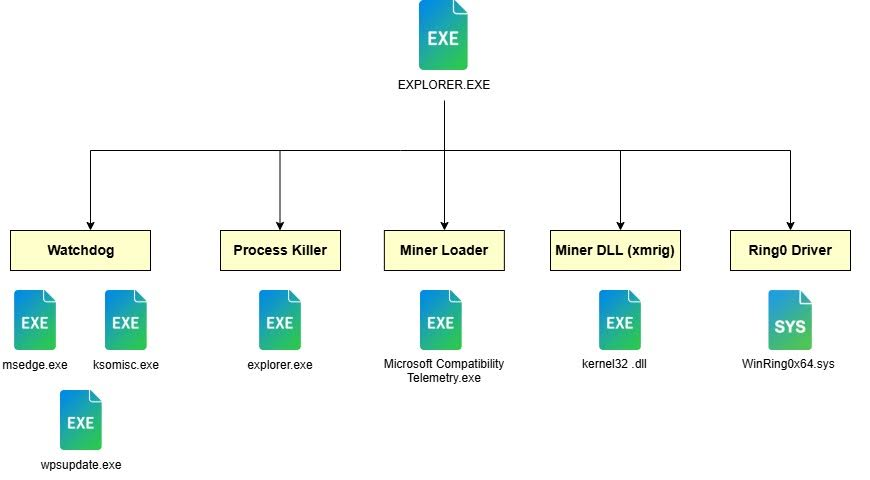
Controller Architecture
Explorer.exe acts as a state machine, switching modes via arguments: none for install, “002 Re:0” for master orchestration, “016” for maintenance, “barusu” for cleanup. This “Brain vs. Brawn” split keeps logic lightweight, delegating mining to “Microsoft Compatbility Telemetry.exe” and enforcement to watchdogs.
A time bomb checks local time against Dec 23, 2025; post-deadline triggers “barusu” to terminate processes (e.g., msedge.exe, ksomisc.exe) and delete files.
Infinite loop (sub_14000D330) seeds randomization with GetTickCount64 to spawn watchdogs like edge.exe, which run “explorer.exe 016”. This Hydra-like cycle resurrects components: if the main crashes, keepers restart it; if keepers die, the main redeploys them.
Process surveillance uses CreateToolhelp32Snapshot, OpenProcess, and K32GetModuleFileNameExW to distinguish malicious explorer.exe processes from legitimate ones and monitor miner health.
Aggressive defense kills real explorer.exe on repeated miner failures, blinding the desktop for re-injection cover.
Decompressed resources yield seven files, including a typosquatting miner wrapper (SHA256: 5936ae20028b79e3ebb58f863960e56f93aed4e7a07f0b39a80205a8a7df5579), space-trick DLLs (Kernesideloadingxplorer.exe), and watchdogs.
Miner uses DLL sideloading: wrapper loads XMRig DLL via GetProcAddress(“xmrig_main”), passes args like –coin XMR –url xmr-sg.kryptex.network:8029.
| File | Role | Technique |
|---|---|---|
| Microsoft Compatbility Telemetry.exe | Miner loader | Typosquatting |
| Kernel32 .dll | XMRig DLL | Space masquerade |
| winRing0x64.sys | BYOVD driver | CVE-2020-14979 |
Creates WinRing0_1_2_0 service, loads driver, opens \. \ WinRing0_1_2_0 handle, sends IOCTL 0x9C402088 to write MSR 0x1A4 (turn off L2 prefetchers). Boosts RandomX hashrate 15-50% by reducing cache thrashing.

WM_DEVICECHANGE listener (DBT_DEVICEARRIVAL, DEVTYP_VOLUME) detects USBs, copies payloads, crafts icon-spoofed LNKs via registry tweak (HKCR\lnkfile\IsShortcut delete). Hides arrows for stealth (input 0).
Ghost killer (SHA256: 51b98f8fb38e822245a1b22864652d7d091dd2f52424786051cbc8131b7e782b) terminates AV via ShellExecuteExW.
Mine to wallet 42DKy5tDGH5MjwWDw2nAj7ZydTsX43cxM5T7zfjPezaEav51eALbqQhDo6ZUgF58tA3s28LnvSTUKTdAZUtqcGXsTBZrDfH via Kryptex pool; low activsideloading/s) indicates testing.
MITRE: T1574.002 (DLL side-loading), T1068 (BYOVD), T1496 (resource hijacking).
Block vulnerable drivers via HVCI/Vulnerable Driver Blocklist; restrict USB access; deny access to mining pools; avoid pirated software. Trellix detects via Trojan-FZTA, Tool.CoinMiner.
Site: cybersecuritypath.com
Reference: Source



