OpenClaw Flaw Enables Website-to-Local Agent Takeover
In a stark reminder of the risks posed by AI agents, a critical vulnerability in OpenClaw. This open-source AI assistant gained over 100,000 GitHub stars in just five days.
This self-hosted powerhouse, now a go-to for thousands of developers, runs locally on laptops, linking to messaging apps, calendars, and dev tools for autonomous actions. Yet any website a developer visits can silently hijack it, no plugins, extensions, or user clicks needed.
Dubbed a “website-to-local agent takeover,” the flaw chain earned high-severity status from the OpenClaw team, who patched it in under 24 hours in version 2026.2.25. Users: Update now.
OpenClaw’s Meteoric Rise and Hidden Perils
Launched as Clawdbot (later MoltBot), OpenClaw stormed developer circles with its web dashboard and terminal interface. It autonomously handles messages, commands, workflows, and even emergent AI networks. On February 15, OpenAI’s Sam Altman hailed creator Peter Steinberger as a “genius” new hire.
Trouble brewed early: Researchers found 1,000+ malicious “skills” in ClawHub, faking crypto tools to steal data. That was supply-chain poison. Oasis’s find hits deeper in OpenClaw’s core gateway, sans marketplace or extensions. It spotlights “shadow AI”: dev tools that evade IT oversight by granting broad local access.
Gateway and Nodes: The Vulnerable Core
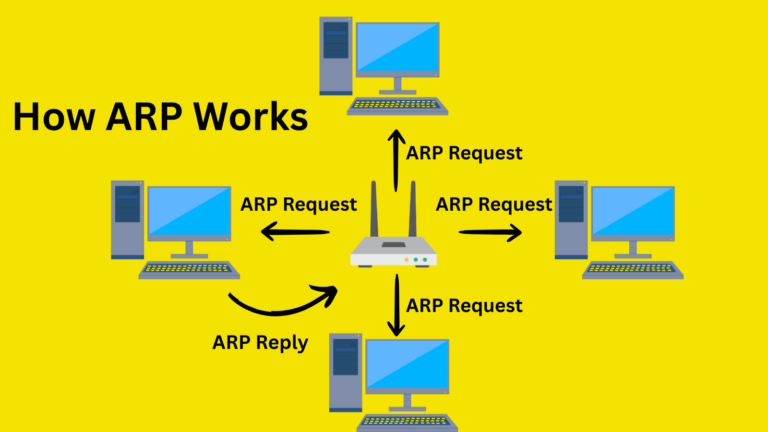
OpenClaw’s gateway is a local WebSocket server managing auth, sessions, configs, and orchestration. Nodes (macOS apps, iOS devices, etc.) register, exposing capabilities such as commands, camera access, and contacts. Auth uses tokens or passwords; it binds to localhost, assuming local trust.
That’s the flaw’s crux.
The Attack Chain: From Browser to Full Control
Imagine a developer browsing, OpenClaw humming on localhost with password auth. They hit a malicious site. JavaScript launches:
- WebSocket to localhost: Browsers allow cross-origin WebSocket connections to localhost, unlike HTTP. The site silently pings OpenClaw’s port undetected.
- Password brute-force: No rate-limiting for localhost. JS blasts hundreds of guesses/second. Common passwords crack in <1s; dictionaries in minutes. No logs, no throttling.
- Auto-trusted registration: Local connections bypass user prompts and are automatically approved as “trusted devices.”
Authenticated attackers wield admin privileges: query the AI agent, dump configs (AI providers, channels), list nodes (devices/IPs), read logs. Escalate? Command Slack searches for API keys and exfil files, runs a shell on nodes, and performs a full workstation pwn via a browser tab.
Oasis’s PoC proved it end-to-end: Password guessed, agent hijacked, all invisible.
Reported responsibly, the patch turns off localhost exemptions, adds rate-limits, and mandates pairings. Kudos to the open-source speed.
Organizational Action Plan
- Inventory AI tools: Scan for OpenClaw, local LLMs shadow AI blindsides.
- Patch urgently: v2026.2.25+.
- Audit agents: Revoke excess creds; limit commands.
- Govern non-humans: Enforce intent checks, JIT access, and audits like Oasis’s platform.
As agents embed in workflows, governance isn’t optional. OpenClaw’s saga warns: Power demands vigilance.
Site: cybersecuritypath.com
Reference: https://www.oasis.security/blog/openclaw-vulnerability