
ResidentBat Android Spyware Linked to Belarusian KGB Operations
A sophisticated Android spyware attributed to the Belarusian KGB, targeting journalists and civil society activists. This implant enables extensive surveillance through physical device access, marking a targeted escalation in state-sponsored digital threats.
Discovery and Background
ResidentBat emerged publicly in December 2025 via a joint investigation by Reporters Without Borders (RSF) and RESIDENT.NGO.
The spyware was found on a journalist’s device post-KGB interrogation, where physical access allowed installation during detention. Code analysis reveals development traces back to at least 2021, indicating long-term investment in this tool.
Unlike remote exploits like Pegasus, ResidentBat demands hands-on deployment: attackers seize devices at borders or arrests, disable Google Play Protect, enable ADB, sideload the APK, and grant permissions manually. This limits mass use but ensures persistence against high-value targets in Belarus’s repressive environment.
Installed ResidentBat grants operators broad access to victim devices. Key functions include exfiltrating SMS messages, call logs, and encrypted messenger data; capturing microphone audio and screen recordings on demand; and stealing local files.
Remote control extends to JSON-configured commands for tasking, status checks, and even DevicePolicyManager.wipeData for full device erasure. Parameters like server address (sars), upload interval (spd), and urgent exfil flag (asp) are pushed from C2 servers, enabling adaptive surveillance.
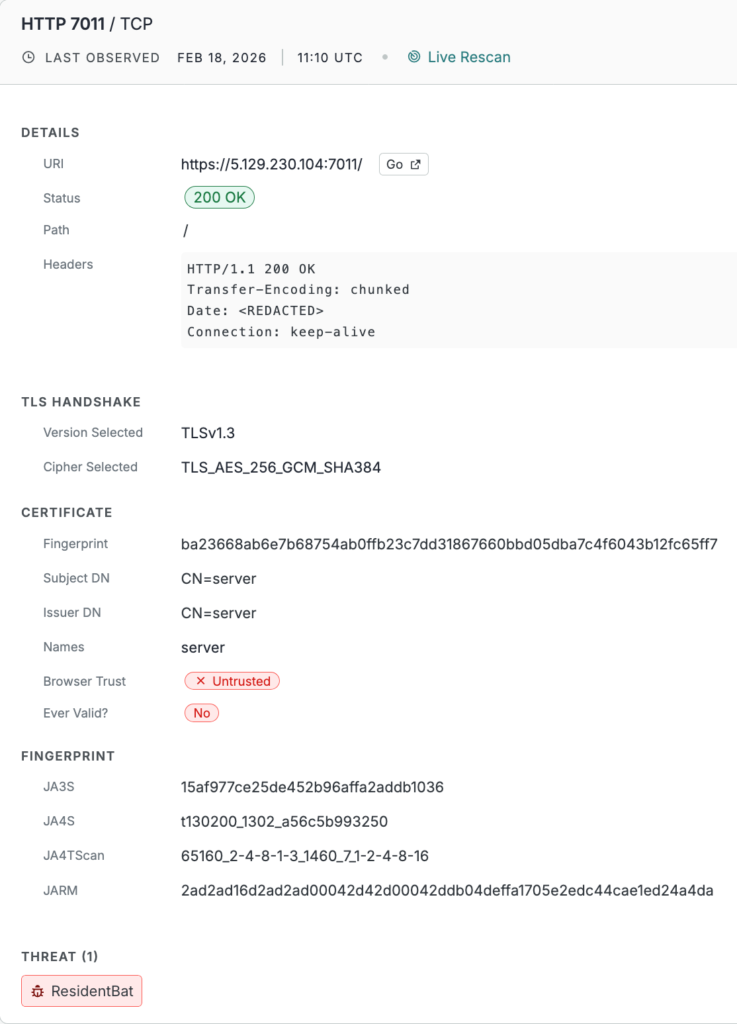
ResidentBat’s command-and-control (C2) servers expose unique traits for global detection. They operate over HTTPS on ports 7000-7257 (plus some on 4022), using self-signed certificates with CN=server and a fixed TLS/HTTP banner hash: 6f6676d369e99d61ce152e1e2b2eb6f5e26a4331f4008b5d6fe567edefdbeaca.
Probing reveals hardening: catch-all 200 OK responses with empty bodies, static Date headers (e.g., Tue, 06 Jan 2026 01:00:00 GMT), and reliance on client certs from the APK, proprietary protocols, and device allowlisting. Certificate reuse across IPs/ports, five distinct SHA-256 fingerprints observed, facilitates clustering.
As of February 2026, Censys maps 10 hosts: Netherlands (5), Germany (2), Switzerland (2), Russia (1), often in ASNs like AS29182 (RU-JSCIOT) and AS210976 (TWC-EU), with SSH on port 22 co-hosted.
| Characteristic | Detail |
|---|---|
| Protocol | HTTPS (TLS) |
| Ports | 7000-7257; 4022 |
| Certificate | Self-signed, CN=server |
| Banner Hash | 6f6676d369e99d61ce152e1e2b2eb6f5e26a4331f4008b5d6fe567edefdbeaca |
Threat Module (THREAT-240) automates hunting with queries like host.services.threats.name = “ResidentBat”. Manual searches use: host.services: (cert.parsed.subject_dn = “CN=server” and banner_hash_sha256 = “6f6676d369e99d61ce152e1e2b2eb6f5e26a4331f4008b5d6fe567edefdbeaca”).
This yields JA3S/JA4S/JARM fingerprints, TLS details (e.g., 1.3 AES_256_GCM_SHA384), and geo/AS distributions for blocklisting. RSF’s APK SHA-256 hashes aid sample correlation on VirusTotal or MalwareBazaar.
Targeted users must prioritize physical security by locking devices, turning off USB debugging, and enabling Android Advanced Protection Mode (AAPM) to block sideloading. Organizations should monitor ADB activity, sideloaded apps, and disabled Play Protect on fleets.
Network defenses focus on TLS to CN=server endpoints in the port range, with alerts on matching certs/hashes. Integrating proactive hunting into SIEMs or firewallneutralizeses this KGB tool at scale.
Site: cybersecuritypath.com



