Sonicwall Firewalls Active Reconnaissance Commercial Proxy Infrastructure
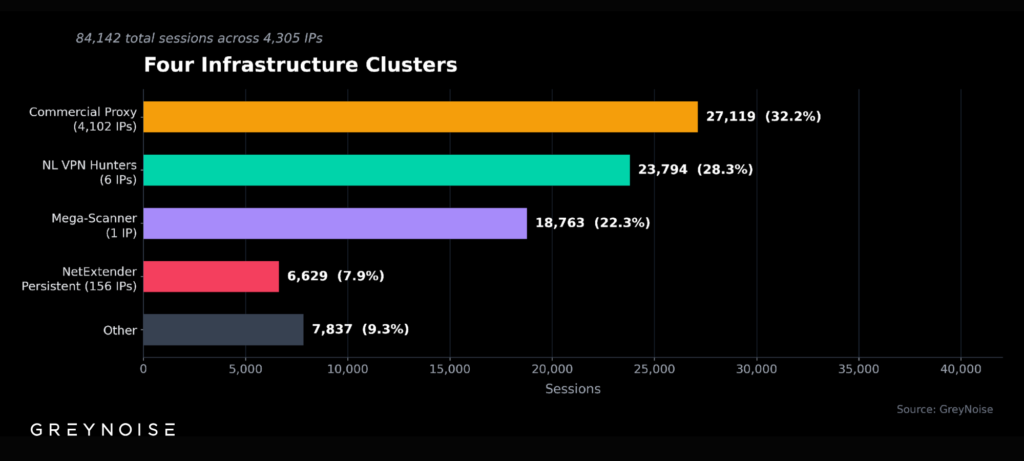
A massive scanning operation against SonicWall SonicOS firewalls from February 22 to 25, 2026, involving 84,142 sessions from 4,305 unique IPs across 20 autonomous systems.
This campaign focused on mapping SSL VPN exposure rather than direct exploits, using commercial proxies to blend with normal traffic.
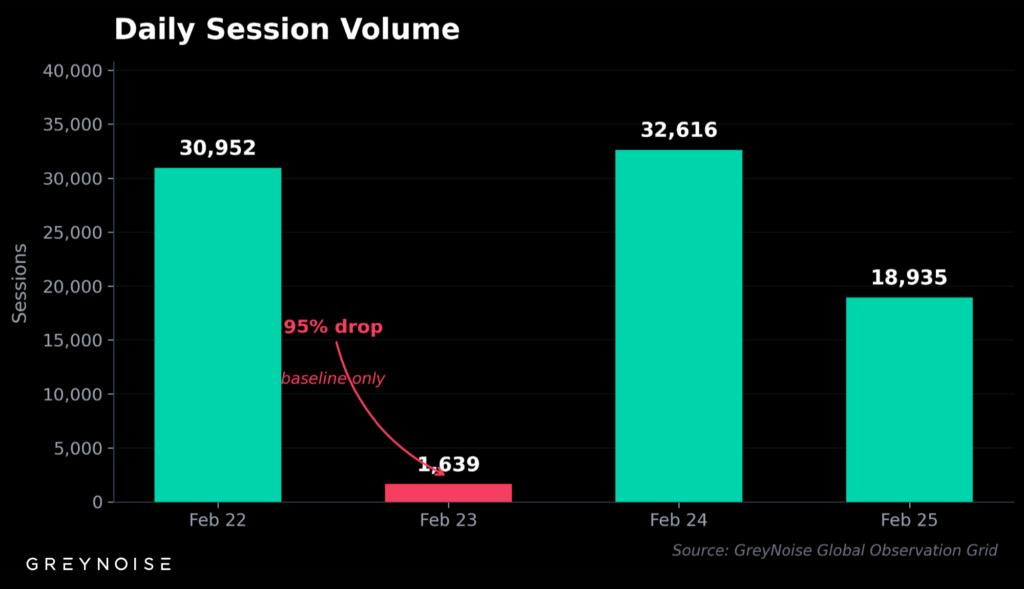
Attackers launched four scanning bursts, peaking at over 7,000 sessions per hour on February 24, with a 31-hour lull on February 23 suggesting deliberate pacing to avoid detection.
Ninety-two percent of probes hit the /api/sonicos/is-sslvpn-enabled endpoint to identify active SSL VPNs, prepping for future credential stuffing. Another 7.9% targeted NetExtender login paths for ongoing credential tests.
A key evasion tactic: 32% of sessions (27,119) routed through ByteZero proxies (bytezero.io), using 4,102 rotating IPs in the 154.208.64.0/21 range at low volumes averaging 6.6 sessions per IP to dodge rate limits.
This proxy’s management platform has been offline since December 2025, allowing unchecked abuse.
Commercial Proxy Infrastructure
Four Infrastructure Clusters :
- Netherlands scanners (28%): Six IPs in AS211736 (Ukraine-registered, Amsterdam-hosted) delivered 23,794 sessions, also probing Cisco ASA gear with identical HASSH fingerprints and custom HTTP services on ports 7001-7003.
- Proxy spray (32%): ByteZero nodes via AS3257 (GTT), in two 7-9 hour windows.
- Mega-scanner (22%): Single IP 130.12.180.29 (AS202412, Germany) hit 18,763 sessions across 20+ ports with rotating user agents.
- NetExtender persistent (8%): 156 IPs ran steady credential tests at 54-72 sessions/hour.
Fingerprint Analysis
A telltale fingerprint dominated 70% of traffic: Chrome 119 user agent with HTTP/1.0 protocol, mismatched for legit browsers and signaling automation.
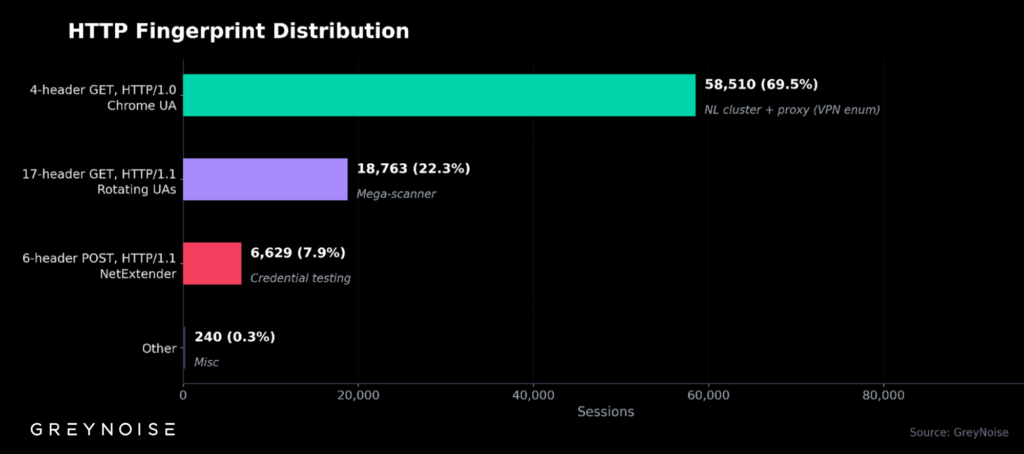
| Fingerprint | Sessions | % | Behavior |
|---|---|---|---|
| 4-header GET, HTTP/1.0, Chrome UA | 58,510 | 69.5% | NL cluster + proxy (VPN enum) |
| 17-header GET, HTTP/1.1, rotating UAs | 18,763 | 22.3% | Mega-scanner |
| 6-header POST, HTTP/1.1, NetExtender | 6,629 | 7.9% | Credential testing |
SonicWall Firewalls Exploitation and High Risk
No widespread exploits occurred; only 0.05% of sessions touched CVE paths, but the recon sets the stage for ransomware plays. SonicWall SSL VPNs remain prime initial access vectors; groups like Akira (250+ victims since 2023, $244M haul) and Fog encrypt networks in under 4 hours post-breach.
This reveals that over 430,000 SonicWall firewalls are exposed publicly, with 25,000 SSL VPNs critically flawed and 20,000 on unsupported firmware. This echoes the December 2025 scans, which hit 9 million Palo Alto/SonicWall sessions from 7,000+ IPs with shared fingerprints.
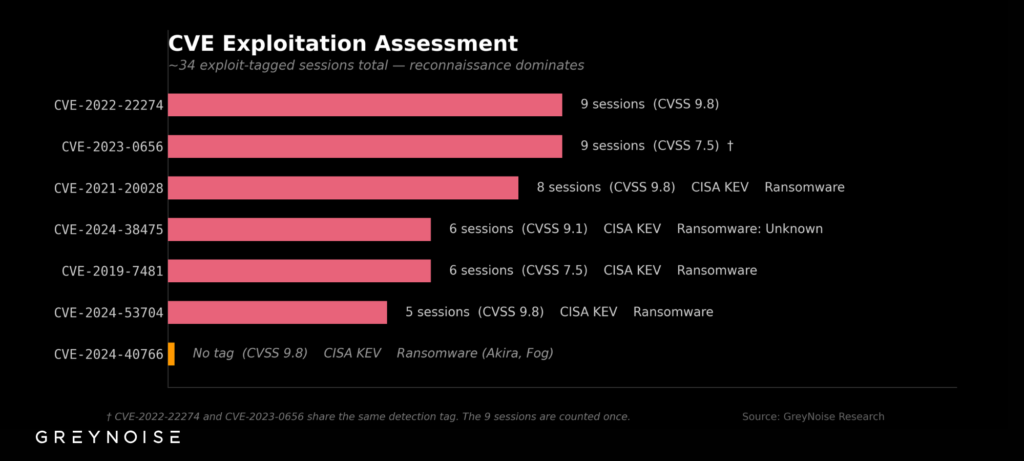
The campaign exposed seven key SonicWall flaws, five of which are in CISA’s Known Exploited Vulnerabilities (KEV) catalog.
Proxy Threat Evolution
Commercial proxies like ByteZero mark a shift from botnets offering 100M+ IPs across 150 countries for scraping, now weaponized for stealth scans.
Unlike static IPs, they rotate to beat blocklists; similar to IPIDEA takedown (550+ groups) or Shadowserver’s 2.8M IP daily VPN brute-force tracking. Low-volume sprays mimic legit traffic, complicating defenses.
Detection and Prevention Steps
Immediate checks :
- Scan logs for /api/sonicos/is-sslvpn-enabled, /sonicui/7/login/, /cgi-bin/userLogin from Feb 22-25.
- Review SSL VPN > Status for suspicious sessions from hosting IPs.
- Patch to SonicOS beyond 7.1.1-7058/7.1.2-7019/8.0.0-8035 (SNWLID-2025-0003); enable MFA.
Ops defenses :