Starkiller Phishing Framework Proxies Legitimate Login Pages to Bypass MFA
In the evolving landscape of cybercrime, a new phishing toolkit called Starkiller is turning heads and raising alarms. Unlike traditional phishing kits that rely on static HTML clones of login pages, Starkiller proxies live content from real websites, rendering defenses like multi-factor authentication (MFA) nearly obsolete.
Marketed as a “commercial-grade” platform by the threat group Jinkusu, this framework operates like a phishing-as-a-service (PaaS) product, boasting a 99.7% success rate on its landing page.
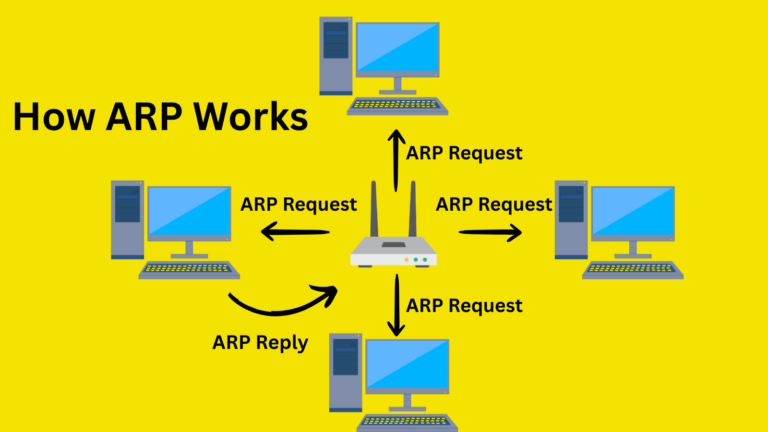
Starkiller’s ingenuity lies in its core engine: a Docker container running headless Chrome. Attackers enter a target’s legitimate URL, such as Microsoft’s login portal, and the system loads the live page, acting as a man-in-the-middle reverse proxy.
Victims see authentic HTML, CSS, and JavaScript streamed directly from the brand’s site through the attacker’s infrastructure. Keystrokes, form submissions, and session tokens flow bidirectionally, all of which are logged for the attacker. No outdated templates means no easy fingerprints for security scanners.
The control panel is polished and user-friendly, rivaling legitimate SaaS dashboards. Operators deploy campaigns with zero coding: paste a URL, spin up a container, and monitor in real-time.
Features include live session streaming, keyloggers, geo-tracking, cookie theft for account takeover, and Telegram alerts for fresh credentials. Analytics track visits, conversions, and graphs enterprise perks for crooks.
MFA bypass is the killer app. Victims enter one-time codes on what appears to be the real site; the proxy relays them instantly, capturing the resulting authenticated session cookies.
Attackers then hijack the session, sidestepping protections designed for static fakes. Extended modules target financial fraud, harvesting credit card details, crypto wallet seeds, and bank info. Fake browser update templates deliver malware, while “EvilEngine Core” promises undetectable links via advanced obfuscation.
URL Masking: The Deception Front Door
Starkiller’s URL masker lowers thebarrier to entry for phishing. Select a brand (Google, Amazon, PayPal, etc.), add modifiers like “login” or “verify,” and generate deceptive links.
It leverages the @ symbol trick to display userinfo before @, prominently masking the malicious domain afterward. Integrated shorteners (TinyURL, etc.) obscure further. A link like “microsoft.com-login” routes to attacker servers, but victims see a pristine Microsoft page in their address bar.
From the target’s perspective, it’s seamless: an authentic rendering, with no visual glitches. Attackers watch via an “Active Targets” dashboard, viewing IP addresses, devices, locations, and live feeds. They can inject prompts or kill sessions undetected.
Email remains the primary vector, mimicking business alerts such as Teams invites. Starkiller harvests emails from sessions to enable lateral spread. Jinkusu fosters a forum for tips, mobile support requests, and updates for v6.2.4. Operators get 2FA logins, Telegram help, and docs ironic for a tool that neuters MFA.
Traditional tools falter: static analysis, blocklists, and URL reputation can’t touch live proxies. Starkiller commoditizes advanced attacks, fueling phishing’s role as top breach vector, said Abnormal.
Defenders must pivot to behavior: monitor anomalous logins, token reuse from odd geos, and identity signals. Inbox-level analysis of email sender reputation, content anomalies, and stops links pre-click. Deploy proxy-aware email gateways, enforce device trust, and train on URL inspection. Tools like behavioral biometrics and continuous session validation add layers.
Site: cybersecuritypath.com