Microsoft has unveiled a major security overhaul for Windows, eliminating default trust in kernel drivers signed under a deprecated cross-signed root program from the early 2000s. This change, rolling out in the April 2026 update, prioritizes drivers vetted through the rigorous Windows Hardware Compatibility Program (WHCP), which scans for malware and verifies OS compatibility.
The cross-signed program allowed third-party certificate authorities to issue Windows-trusted certificates with minimal vetting, leading to private key abuse and credential theft that exposed systems to kernel-level attacks. Although deprecated in 2021 with expired certificates, these drivers remained broadly trusted, creating a persistent vulnerability in the Windows kernel.
Kernel drivers operate at Ring 0, granting them unrestricted access to disable antivirus, tamper with endpoints, or escalate privileges prime targets for malware like BYOVD (Bring Your Own Vulnerable Driver) attacks. Security experts hail this as closing a 20-year-old hole, shrinking the attack surface without a single breach trigger, but part of ongoing cleanup.
Starting April 2026, the policy hits Windows 11 24H2, 25H2, 26H1, Windows Server 2025, and all future versions. It launches in “evaluation mode,” auditing driver loads over 100 hours (Windows 11/Server) and 3/2 boot sessions to check compatibility.
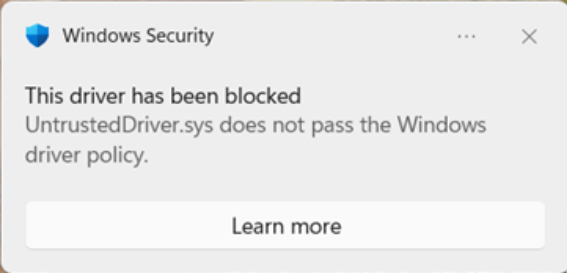
If only trusted drivers (WHCP-signed or allow-listed) load, enforcement activates, blocking others with user notifications. Untrusted cross-signed drivers trigger a reset, keeping systems safe for rare legitimate uses while enabling protection elsewhere. Microsoft curated the allow list from two years of billions of driver load signals, preserving widely used, reputable legacy drivers.
This table highlights why WHCP sets a higher bar, reducing risks from unvetted code.
Admins can override via Application Control for Business (formerly WDAC) policies, signed by Secure Boot PK/KEK keys for custom or internal drivers. This suits confidential scenarios without WHCP submission, maintaining security isolation.
However, exceptions like the allow list are temporary; Microsoft plans gradual phase-out.
For enterprises, this disrupts hidden legacy dependencies in IoT, medical gear, or factories using unupdated drivers. Preparation involves inventorying drivers, testing critical systems, querying vendors for WHCP updates, and planning App Control policies.
While not a silver bullet malware adapts this narrows blast radius, forcing cleaner ecosystems. It aligns with Microsoft’s multi-year attack surface reductions, from Secure Boot to HVCI.
In threat intelligence terms, expect attackers to pivot from stolen cross-signed certs to WHCP evasion or policy bypasses. Organizations should monitor April updates closely.
Site: cybersecuritypath.com



